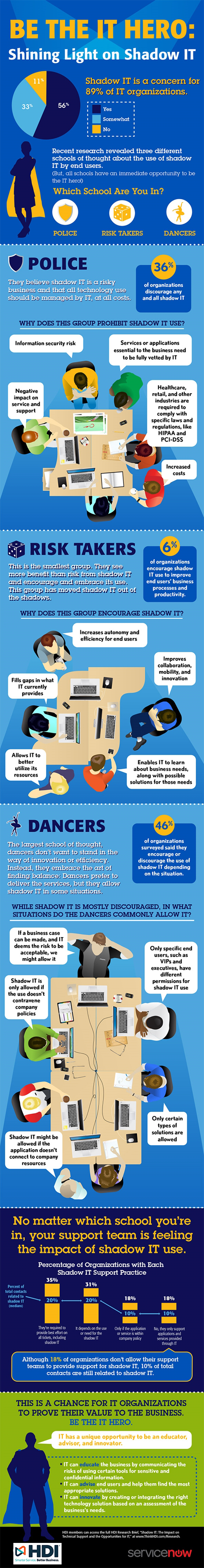
From students to executives, finding solutions to improve efficiency, productivity, and communication has become vital. These end users are trying to excel in their work, and while they don’t mean to cause harm, in most organizations this desire leads to the use of applications, services, and data storage and sharing beyond IT's boundaries. This practice, known as “shadow IT,” walks a line that information security officers are uncomfortable with, and it’s having an obvious impact on technical support teams. The good news is, there are opportunities for all support organizations, regardless of their stance on shadow IT.The current world of IT is complex, and the best set of processes for your organization might be a combination of frameworks and methodologies rather than just one. This infographic illustrates data on how organizations of all sizes and across industries are using a comination of frameworks and methodologies in their support operations.