Date Published January 26, 2018 - Last Updated December 13, 2018
James will present his research on how the service desk can help manage security incidents at HDI 2018.
Learn more!
In the more than 20 years I’ve been working in the cybersecurity and service desk industry, I’ve never before witnessed so many changes in our digital landscape. From digital transformation to the cloud and IoT, we’re seeing radical changes in the technology that we use, as well as how we use that technology. We’ve also seen an alarming increase in security incidents.
I’m convinced that one way to stem the tide of cybersecurity incidents is to better involve the service desk in security efforts. To that end, I’ve had my organization, CompTIA, conduct a survey into how the service desk can be a major factor in helping manage security incidents. Let me start with some background about technology changes and some serious problems before I talk about the kill chain and further discuss my conclusions.
One way to stem the tide of cybersecurity incidents is to involve the service desk in security efforts.

Radical Changes in Technology
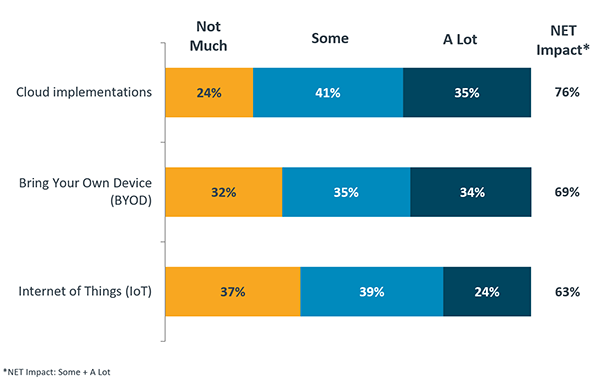
First, our survey started by asking over 600 service desk managers and professionals about the major changes service desk professionals have seen in the past few years. The figure below shows the three radical technology changes that have impacted the service desk:
Cloud technologies have impacted us the most, especially because cloud implementations have really increased over the past 18 months. Cloud has brought with it a decentralized IT environment; now each department in an organization is sourcing its own IT. As a result, we’re witnessing:
-
The evolving end point: It’s not about just mobile devices and PCs anymore. We’ll see end points continue to morph even more radically in the near future.
-
Shadow/decentralized IT: Call it what you want, but departments all around your company or organization are sourcing their own IT solutions. Get used to it.
-
The dissolving perimeter: Yes, firewalls still exist, and they’re important. But they only get you so far. Now, you need to protect—and backup—resources on various sides of the firewall. We’ve always worried about the “insider threat.” But now, there really is no strong demarcation between “inside” and “outside” when it comes to IT.
Silo-Based Communications and Interstices: The End User
We’re seeing too many organizations continue to treat IT and security workers as a communications silo. Today’s hackers are finding ways to “hide in plain sight” by exploiting gaps or interstices that occur when one technology (e.g., an IoT device) is connected to another (e.g., a database within a company). Hackers love to exploit communications silos and the gaps that result. The solution is to integrate the service desk with cybersecurity efforts.
The most significant interstice that exists today is where end users—and all of their devices— connect. We’ve been saying for years that end users are the primary security problem. Yet, isn’t it interesting that few cybersecurity professionals really use service desk and service desk data to solve problems?
Protecting the End User: Who Knows How to Do That Better?
It’s worth saying again: All of the major technology changes we’ve seen tend to center on the end user. It only stands to reason, then, that cybersecurity professionals would focus on end-user problems. The service desk has focused on discovering and resolving user issues for decades now.
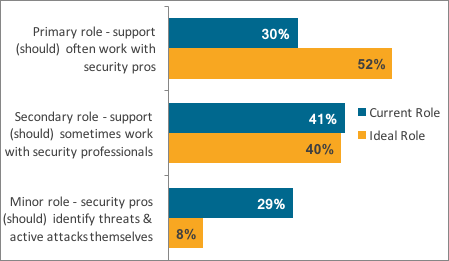
Yet, only 30% of the service desk professionals we surveyed indicated that they work regularly with security professionals in their organization. Only 41% found that they worked with cybersecurity professionals on a less-regular basis, as shown in the figure below.
Finding a Model to Combat the Advanced Persistent Threat
Organizations today are trying to deal with the Advanced Persistent Threat (APT). An APT is a “low and slow” attack waged by a well-funded group of individuals. Many models exist that try to explain how various gangs of individuals—including state-sponsored and company-sponsored actors—infiltrate systems. Around 2010, several Lockheed Martin employees created a model called the Cyber Kill Chain, which is outlined in the figure below.
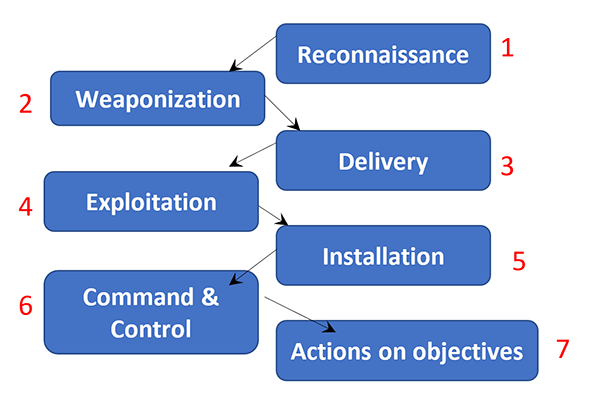
Over the years, cybersecurity pundits and others have debated the relative strengths and weaknesses of this model. It’s not a perfect model. But, it’s a good starting point because it helps companies create a custom security framework that helps outline how to find, respond to, and contain IT security incidents. I’ve found that if you don’t create a customized, model for your company, then you really won’t be able to solve your company’s security problems.
Survey Results: Including the Service Desk
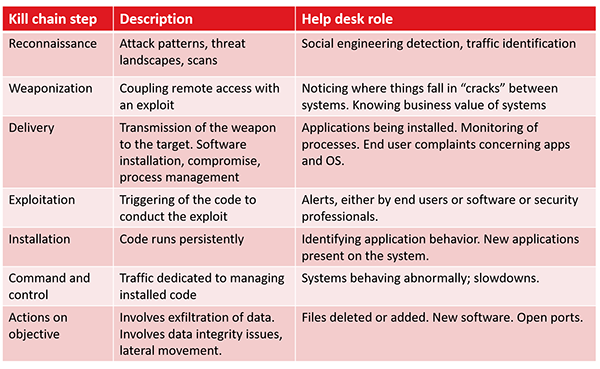
One respondent to our survey who works in the finance sector wrote that “Most organizations I’ve looked at don’t do data analysis on their tickets for patterns which would indicate a problem.” This means that most organizations will never be able to conduct the proper mapping of each theoretical “kill chain” step to real activities, as found in the figure below.
I’ve also been talking with quite a few CIOs, CTOs, and security directors about this concept. One of the people I spoke with works for one of the top retailers in the world. When I asked him about the service desk and security, he wrote back the following:
“In a previous organization . . . had had some very sensitive data exposed by malware which resulted in the executive leadership wanting us to find and destroy all malware of any type. After about six months of using a bunch of techniques to find and eliminate all malware (including stuff like potentially unwanted software), the volume of help desk tickets at that organization reduced by nearly 60% and there was a clear causal relationship. We discovered when we dug deeper that all sorts of problems like “printer” issues were in many cases a symptom of a host having malware of some sort on them.
So bottom line is I think there is a lot of untapped synergy between help desk and security where both groups could help each other.”
I can’t help but think that my cybersecurity friend could have saved a lot of time at the beginning of his malware “search and destroy” mission: Imagine if he had started by first reading service desk tickets. I think he would have seen the large spike in printer and end user issues and would have found the problem more quickly. This is just one example of how careful analysis of service desk and the service tickets can help improve overall cybersecurity. After all, few sectors of IT know more about how to analyze data and discover trends than service desk managers.
Positive Examples
Our survey found some very good examples of effective service desk and cybersecurity interaction. One individual shared the following:
“Phishing attacks were running rampant in our organization due to a bug with our filtering appliance. Our help desk recognized the issue right away and implemented special training for all staff to identify potential attack vectors.”
Another wrote:
“Tier II and III personnel . . . get involved with application developers to resolve the issues before they can be exploited. Service technicians doing vulnerability scans can isolate affected systems and take them offline until patching can be done.”
These are outstanding examples of how service desk and service desk professional knowledge can be distributed usefully throughout an organization.
Need for Improvement
Still, roughly half of the organizations continue a silo-based approach to security. One respondent wrote:
“Little no nothing can be done as we support a government organization. All security matters are handled at levels higher than the help desk / service desk.”
Yet another wrote about how her organization suffers from silo-based communication:
“It's like Gordon Ramsay's Kitchen Nightmare where the chef is the expert at making an awesome burger but the owner wants the chef to make some crappy burger instead because the chef is being paid by the owner.”
Start with the Service Desk
We constantly hear how organizations want to be proactive, rather than reactive, when it comes to security. Organizations are trying to mature their security operations so that the move from traditional alert-based and signature-based approaches to more sophisticated solutions. We want to detect problems across the attack lifecycle or kill chain. I propose that starting at the service desk is, really, a fundamental step. It’s not a nice to have. It’s a must have.
James Stanger is a respected authority in security, service desk, open source, ITSM, networking, and IT certification. Over the past 20 years, he has consulted with corporations, governments, and learning institutions worldwide, including IBM, Symantec, the US Department of State, the US Department of Defense, the Scottish Qualifications Authority (SQA), and the United Arab Emirates Cultural Division. He has published dozens of books and articles concerning IT, and developed education and certification programs used around the world. Follow James on Twitter @jamesstanger.